The topic of I ignored IPv6 for years, and now my home network is paying the price is currently the subject of lively debate — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
Until recently, IPv6 was perpetually on my “deal with it later” list. I’m sure it’s the same story for many home lab enthusiasts. We all know IPv6 exists, and that IPv4 is living on borrowed time, which has been continually extended by various NAT workarounds that were never meant to be permanent fixes. As long as everything on my network kept working, IPv6 felt easy to ignore. Then, my ISP quietly transitioned to IPv6, and I realized it left a security hole in my firewall rules that I hadn’t anticipated.
Google shared that on March 28, 2026, more than 50% of users accessing their services did so over IPv6. It’s the first time that figure has crossed the majority threshold in the 18 years since Google began tracking it. It took almost three decades for IPv6 to reach that milestone, but it marks the moment when IPv6 is definitively here, not just something off in future.
IPv4 has long outstayed its welcome, yet IPv6 still isn’t the norm. What’s happening?
NAT (Network Address Translation) was originally invented to conserve IPv4 addresses. Rather than every device on a network needing its own public IP address, they could all share the same one thanks to NAT. It wasn’t intended as a security feature, but it ended up increasing home network security as a positive side effect. Devices using NAT are invisible to the outside world by default, since unsolicited inbound traffic hits the router and gets dropped before touching any internal devices. It’s not the same as a firewall, but it does have a similar effect in this regard.
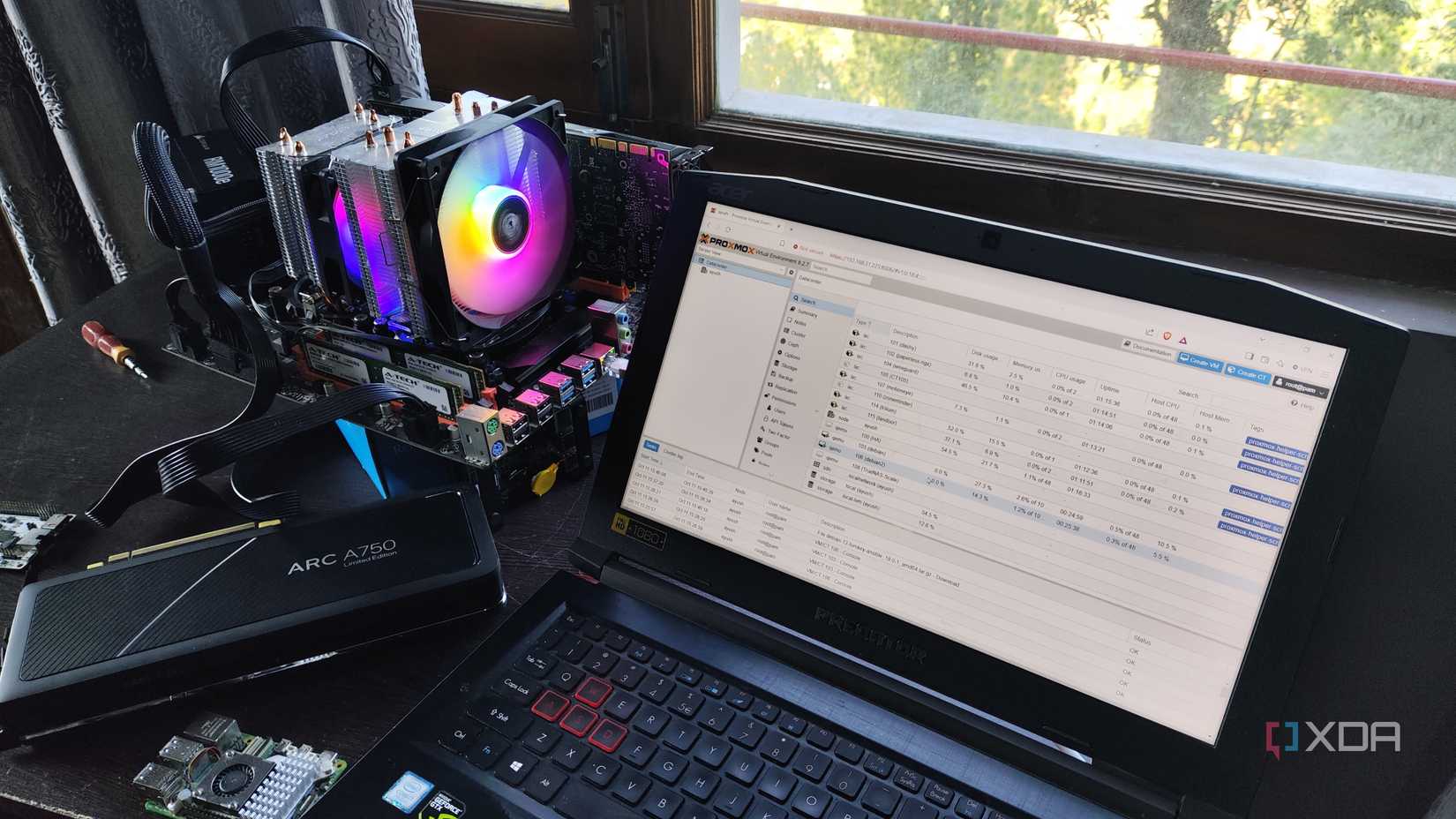
My previous router had IPv6 disabled, and all my firewall rules were configured for IPv4. I switched to a new router, and it had IPv6 turned on by default. I installed the new one, and it seemed to work fine, so I called it a day. Little did I realize that all of my devices were now connecting to the internet with their own IPv6 addresses, effectively bypassing my firewall, which was only filtering for IPv4. Apparently, this is a common “gotcha” that trips up many people, though casual users who aren’t hosting anything probably won’t be affected. It’s only something to be wary of if you’ve configured custom rules that are IPv4-only and rely on them for the security of the services you expose.
The direct exposure of my home lab devices to the internet wasn’t catastrophic. All of those systems still have a software firewall installed, which blocks incoming IPv6 traffic by default, so nothing nefarious got through in the interim. But I did take the time to update the router’s rules as soon as I noticed the change. I kept IPv6 enabled, as that’s a future we can’t ignore anymore, but I also configured a simple rule that drops any incoming IPv6 traffic, except for established and related connections. This is a straightforward WAN rule to add to pfSense or OPNsense. It varies by consumer router, but most have an IPv6 firewall that can be toggled on.
There’s no opt-in toggle for IPv6. Your ISP already supports the new address scheme and may already be delegating IPv6 prefixes to your router. If your home lab was mostly configured with IPv4 in mind, it’d be worth a quick peek to see if your firewall is filtering traffic as you expected. Most people’s networks are probably fine, especially if they’re running default router settings and don’t host any services, but if that’s not you, it’s worth testing your network security before something else does.
TP-Link Archer BE800 is a powerful WI-Fi 7 router that sports a blazing-fast tri-band BE 19000 connection and multiple 10Gbps wired ports.
Why it matters
News like this often changes audience expectations and competitors’ plans.
When one player makes a move, others usually react — it is worth reading the event in context.
What to look out for next
The full picture will become clear in time, but the headline already shows the dynamics of the industry.
Further statements and user reactions will add to the story.
