The topic of Why I ditched Cloudflare Tunnels for Tailscale and Caddy on my homelab is currently the subject of lively debate — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
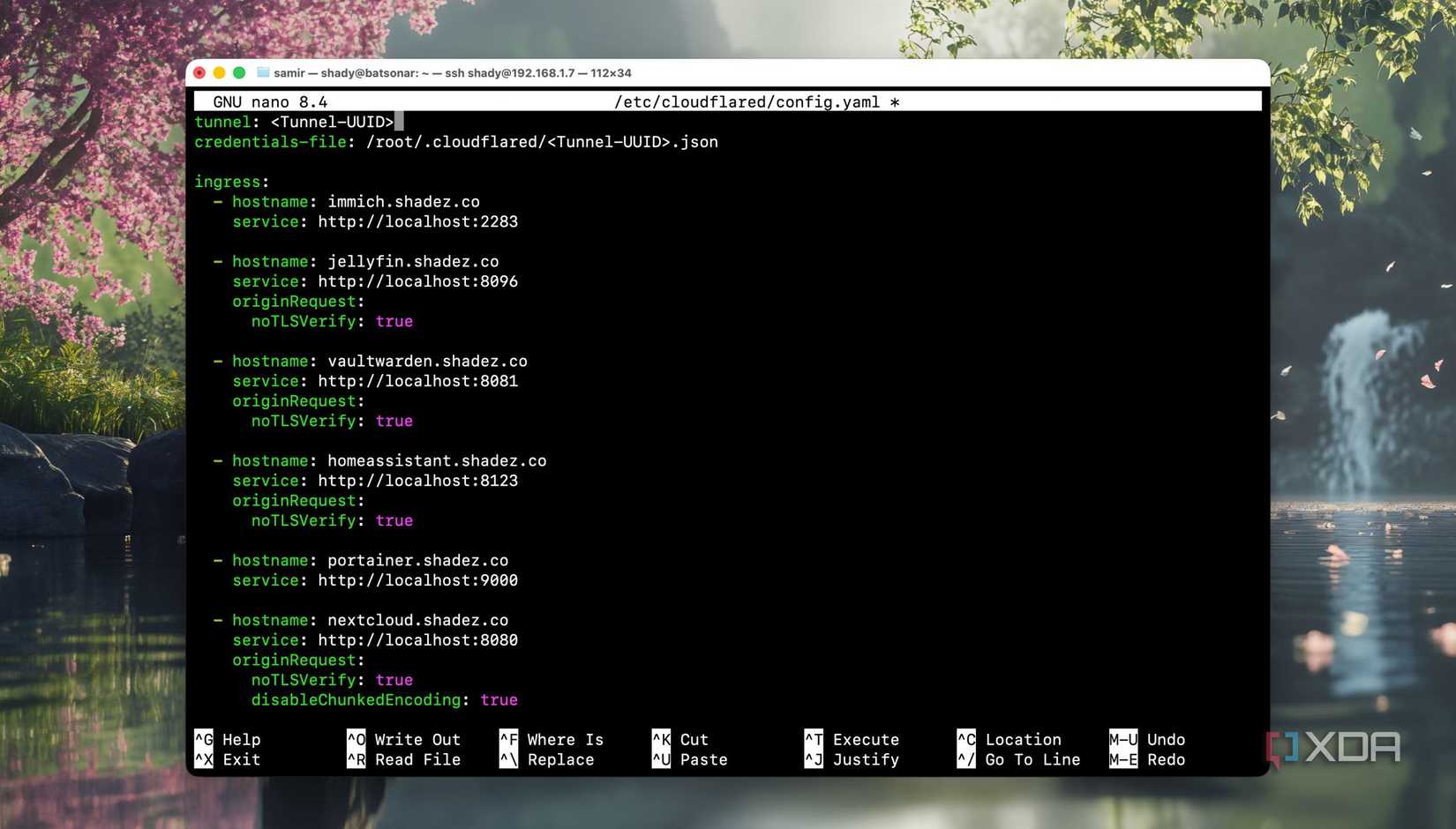
Setting up Cloudflare Tunnels for the first time in my homelab felt like unlocking a kind of superpower. I didn’t want to open ports, deal with SSL renewal hassles, or wrestle with dynamic DNS. With Cloudflare Tunnels, I could access my self-hosted instances of Immich, NextCloud, Jellyfin, Vaultwarden, and other services from anywhere.
I happily mapped all of them to my subdomain and figured it was the best way to run my homelab. Over time, small frustrations accumulated until they became impossible to ignore. Here’s why I switched from Cloudflare Tunnels to Tailscale and Caddy — and haven’t looked back.
Say goodbye to the hassles of port forwarding with this secure, easy-to-use alternative.
Like many homelab beginners, I started by exposing my Pi-hole dashboard. Soon, I had Home Assistant, Jellyfin, Immich, Portainer, and a few other network tools like NetAlertX, all mapped to subdomains via Cloudflare Tunnels.
I often notice latency when accessing my self-hosted services away from home. It was tolerable for viewing dashboards, but it became a real problem when using Home Assistant, streaming videos remotely, and transferring files.
I have always felt anxious about the Terms of Service that Cloudflare lays down for Tunnels. The free tier discourages streaming large video files through the tunnels and is often considered a “gray area.” Though penalties are rare, an abuse report can take down my services at any time. That low-key fear existed like a mild headache.
On the free tier, I couldn’t upload files larger than 100 MB at a time. So transferring files from my laptop to the home server really took a while. On top of that, the outages also took down my access to my homelab. In the end, I realized I was the only one accessing my homelab remotely.
I realized I didn’t really need to expose my homelab to the internet, at least not all of its services. I wanted to access my self-hosted services, dashboards, and home server remotely. Tailscale assigns every device a private IP and a MagicDNS hostname within your tailnet.
Setting up Tailscale on my phone, computer, and home server took less than 15 minutes. Each device got a specific IP address in a private mesh network, and I enabled the MagicDNS as well. After that, I can reach my home server from anywhere using Tailnet names.
The free tier is sufficient for my homelab and the services running on it. Yes, Tailscale still has a third-party dependency, but I’ve had few outages so far. The best part is that my devices get to communicate over WireGuard even if the coordination layer hiccups.
My homelab and self-hosted services were no longer publicly accessible. I didn’t have to change anything on my router or open ports. Since I am the only one who can remotely access my homelab, Tailscale checks all the boxes for me.
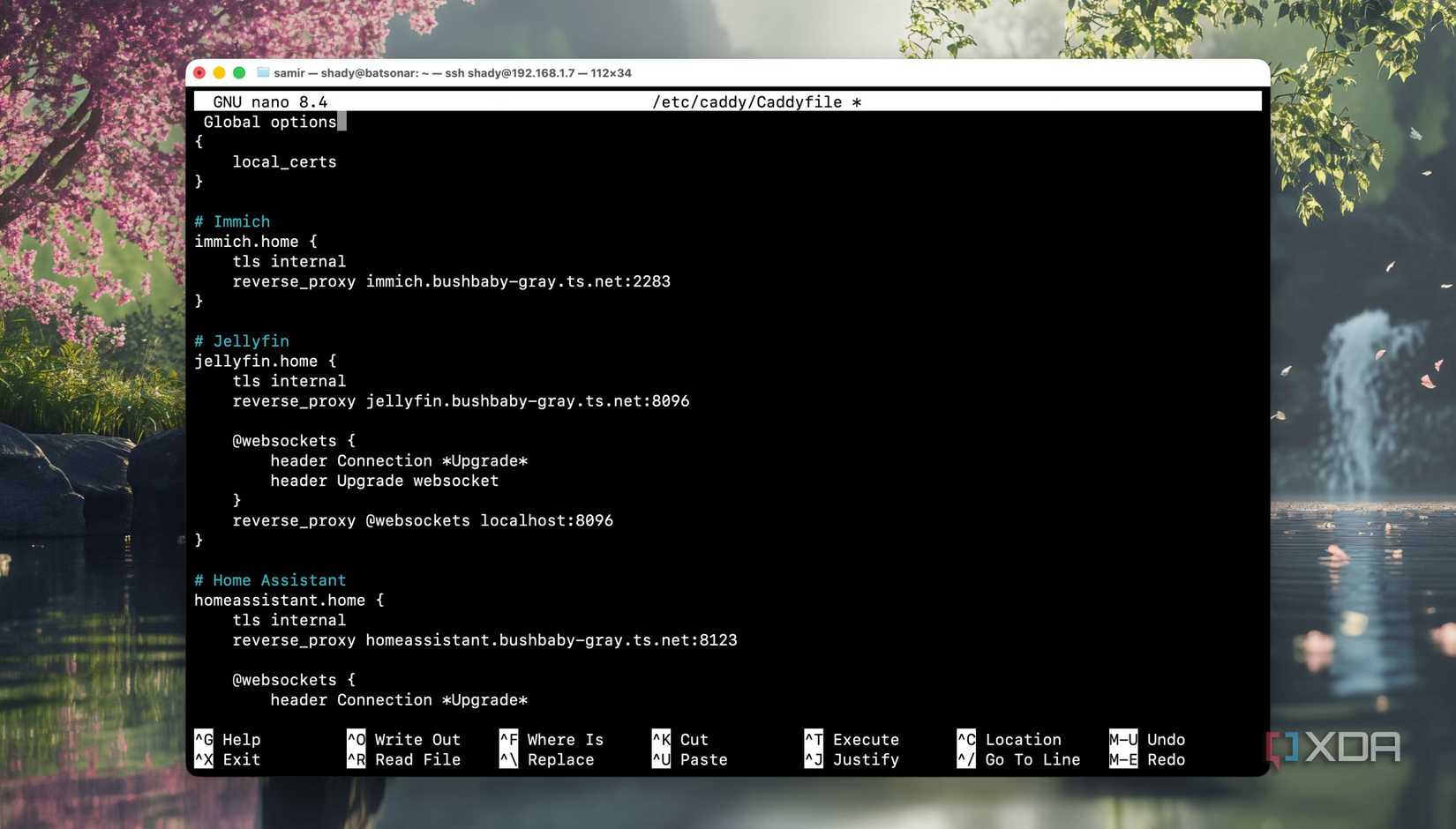
Browser security warnings were annoying enough, but Immich’s mobile app refused to work with plain HTTP. So I added Caddy as an internal reverse proxy. It handles TLS termination on port 443 and issues internal certificates through its own Certificate Authority. Then, it routes everything by hostname.
That frees me from having to remember the IP address and port for every service running in my homelab. Once I trusted Caddy’s root CA on all my devices, the browser warnings disappeared everywhere.
I battled with NGINX configs before, and wasn’t going back to using it as a reverse proxy. Traefik would make sense if I were running Docker Swarm with dynamic service discovery while running dozens of containers. But I have a stable and small stack.
Lastly, I pointed Caddy at Tailnet names instead of hardcoding the IP addresses. Since it resolves hostnames dynamically, IP address changes don’t break anything.
I finally have a stack of self-hosted services that I can access remotely without an issue. All thanks to Tailscale and Caddy, for there’s no public footprint of my homelab anywhere. Also, I haven’t experienced any outages since my setup doesn’t depend on third-party services.
The only drawback is that I had to give up the simplicity of simply sharing the access or links to media in my homelab. However, I run the homelab for myself and not for others.
If I ever have to share a file or folder with public access, I prefer to serve it through Tailscale Funnel. After all, it’s my personal homelab, and your use case might be different.
I’ve made the switch from Nginx Proxy Manager to Caddy, and I’m not looking back.
Switching to Tailscale and Caddy changed the way I think about remote access. I no longer publish services in my homelab publicly and then try to secure them. Instead, I keep them private and connect to them securely. This setup feels leaner and safer, and it aligns with how I want to run my homelab.
Cloudflare Tunnels were the wrong long-term solution for me. After using Tailscale and Caddy, my homelab no longer feels like it’s hosted on the internet.
Tailscale is a tool that allows you to create specific network connections so you can remotely access resources within a private network.
Caddy is a powerful server, reverse proxy, and more, with automatic TLS certificate provisioning
Why it matters
News like this often changes audience expectations and competitors’ plans.
When one player makes a move, others usually react — it is worth reading the event in context.
What to look out for next
The full picture will become clear in time, but the headline already shows the dynamics of the industry.
Further statements and user reactions will add to the story.
