The topic of Your NAS permissions are probably a mess, and a single flat share fixes it is currently the subject of lively debate — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
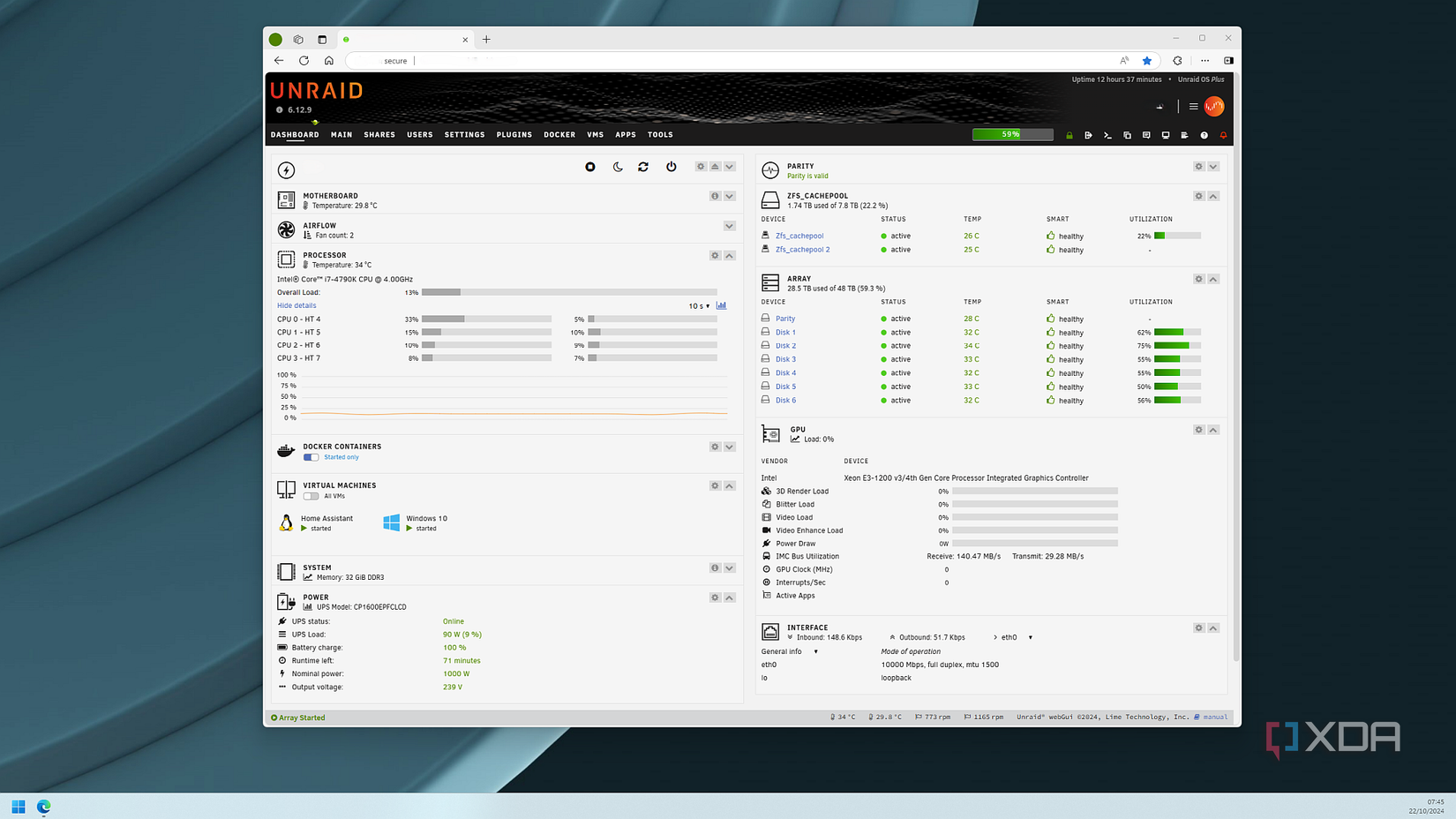
Network-attached storage (NAS) becomes the central part of most home labs and smart homes. Even if you’re not running stacks of used enterprise gear, there’s a good chance you have a NAS server storing all your data, be it documents, backups, media, and other files. What you may not know is how to best use permissions, and if you go about this the wrong way, you could end up overcomplicating something that really should be the simplest part of the puzzle.
It’s not necessarily the fault of the end user, as most NAS operating systems — and yes, I’m including those from turnkey brands like Synology and Asustor — don’t adequately explain what permissions do and how best to approach it. Don’t get me wrong, it’s easier to set up permissions in DiskStation Manager than TrueNAS SCALE, but as a general rule, NAS setups are often plagued by the same recurring issue. Spend a couple of minutes searching NAS communities, and you’ll see just how prevalent the permission problem is.
With a NAS, you can quickly (and easily) create a deeply nested folder structure, have multiple overlapping user groups with countless Docker containers running, and conflicting access control lists (ACLs) that can cause a myriad of problems or simply be too convoluted to look at. Instead of fixing and adjusting existing permissions, some may even create entirely new groups and users as a band-aid. It’s ironic in a way since a NAS is designed to simplify storage, but it can often be the source of frustration.
Before you sound off in the thread below about how it’s not the fault of NAS software developers, I absolutely agree with you. It’s actually how people go about planning out permissions. The problem is that they largely don’t do any planning at all. NAS setups are generally overengineered from the get-go, built on assumptions that don’t really hold up once other user accounts start to use the network storage. One way to overcome this is to flatten shares to dramatically reduce complexity.
It may be challenging to think about simplifying permissions instead of building out complex structures to encompass what you wish to achieve with the NAS and wider network, but it’s the way to go if you don’t wish to pull your hair out. Creating a primary share and some subfolders with specific permissions may sound like the right approach for network storage, but this will introduce several problems further down the line. First, permission inheritance can prove difficult to track when you’re working with folders that could even be misconfigured to override expected permissions.
Then there’s the issue of overlapping groups. Let’s say John belongs to two groups, each with different permissions on the same folder. Which takes priority, and which permission will actually apply? Usually, this isn’t an issue since deny will override allow when conflicts arise, but it could prove troublesome to diagnose when problems relating to storage are raised. John may not be able to access a specific folder, and when troubleshooting, it’ll take longer to parse through all the unique permissions.
It’s easy to consider what’s to come when first setting up a NAS. Instead of thinking about what this network storage will actually solve on the LAN, one can get caught up in designing everything for hypothetical scenarios and edge cases. The system is then optimized to be flexible for adjustments and refinements instead of being usable as network storage. macOS, Linux, and Windows all use more traditional localized storage structures with a few folders for different file types to aid organization, but replicating this on NAS is a bad idea.
Storage organization and access control don’t have to be coupled as they are on a PC. A flat share structure can really save the day when it comes to dealing with complicated NAS permission sets. Instead of cramming everything into one all-encompassing share, as I did on my first NAS, it’s better to form multiple top-level shares, each with a consistent access policy that’s inherited by all subfolders. Similar to how hypervisors allow for a segmented homelab, multiple top-level shares help to keep stored data isolated.
I started with just one share, which held everything, but I eventually made a few, each dedicated to storing specific data. A share is available for backups, another for media, a third for security footage, and so on. Not only does this help keep things simple for user permissions, but it also helps for services and apps that require access to the NAS. I can open up specific shares to each self-hosted app. It keeps it simple. If I assign someone or a service to a share, I know that access will unlock everything within it.
When adding new users and groups, permissions can be set on the share level. Should I need to revoke access for some reason, this is just as simple as setting up a fresh account. It’s easier to troubleshoot should something go wrong, and because there are fewer moving parts involved, the system feels less fragile. Most NAS applications don’t require highly granular permissions. We’re not forming a system primed for a huge enterprise business with thousands of employees.
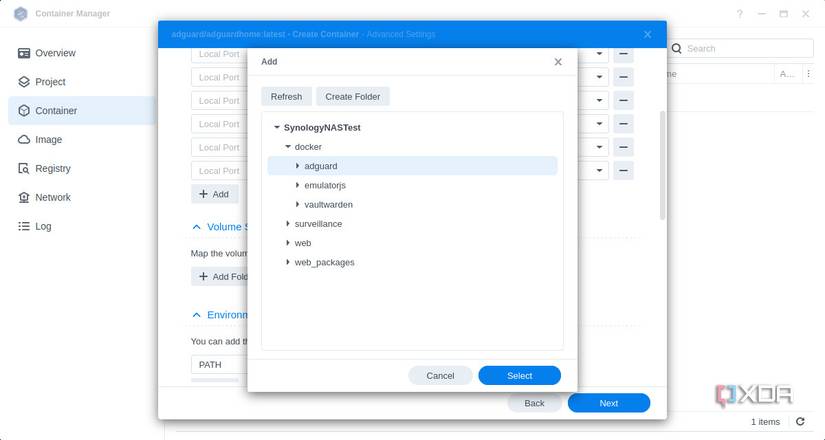
It’s pretty easy to make the move to a flat structure. All that’s required is a quick audit of the existing share and permission setup. Note everything. Identify which folders have unique settings applied and which simply inherit from the share. It’ll be immediately clear which folders can be grouped under a single access policy. Then split up all your data. Media, backups, personal, and security are good places to start for self-hosting media streaming, home surveillance, and automated backups.
Be sure to use groups instead of setting permissions for each user. This keeps things simple and allows the migration of users between groups without having to worry about what permissions may be set for different accounts. The most vital step? Document everything. Be it a simple document file, note, or even part of a self-hosted Gitea repository, make sure you have your NAS permissions structure noted for future reference. You’ll thank your past self multiple times in future.
While it may sound weird, this setup works well when you have a single node and a bunch of unprivileged LXCs
Why it matters
News like this often changes audience expectations and competitors’ plans.
When one player makes a move, others usually react — it is worth reading the event in context.
What to look out for next
The full picture will become clear in time, but the headline already shows the dynamics of the industry.
Further statements and user reactions will add to the story.
