The topic of I never configure a home firewall without these three rules, and they stop the… is currently the subject of lively debate — readers and analysts are keeping a close eye on developments.
This is taking place in a dynamic environment: companies’ decisions and competitors’ reactions can quickly change the picture.
Being connected to the internet has always been slightly dangerous, but in the age of automated scanning and AI, it’s never been more so. Network security is something many assume their router is going to handle on its own, if they think about it at all, but the myth of being too small to be worth targeting is long over. You should have a firewall to protect your network from external and internal threats, and it’s one of the first things I set up when putting together a new home network .
And while setting up VLANs and other advanced networking tools is useful, they don’t matter if you haven’t properly secured your network. I like to stop threats before they become an issue, and set up this trio of rules and tools as a first step. They stop traffic coming from known bad actors, reduce the threat of devices inside my home network betraying me, and stop automated scripts from hammering through my defenses. The best part is that they take minutes to set up, so you can start from a position of strength as you set up the rest of your home network.
If you didn’t already know that your ISP router is trash, consider this your pearl of wisdom for the day. And I mean trash, with slow update cadence, vulnerabilities that don’t always get patched out, default settings that can be deduced from the MAC address, and more. They’re barely suitable for getting your Wi-Fi up and running, let alone keeping you safe on the internet.
You don’t have to go the route of building your own router and firewall, but it’s another thing to think about getting, just like adding window locks or a deadbolt makes the physical entrances to your home safer once installed. The better ones also act as an alarm system, letting you know that attackers have been poking around but didn’t get in, so you can decide which other methods to add to the security setup.
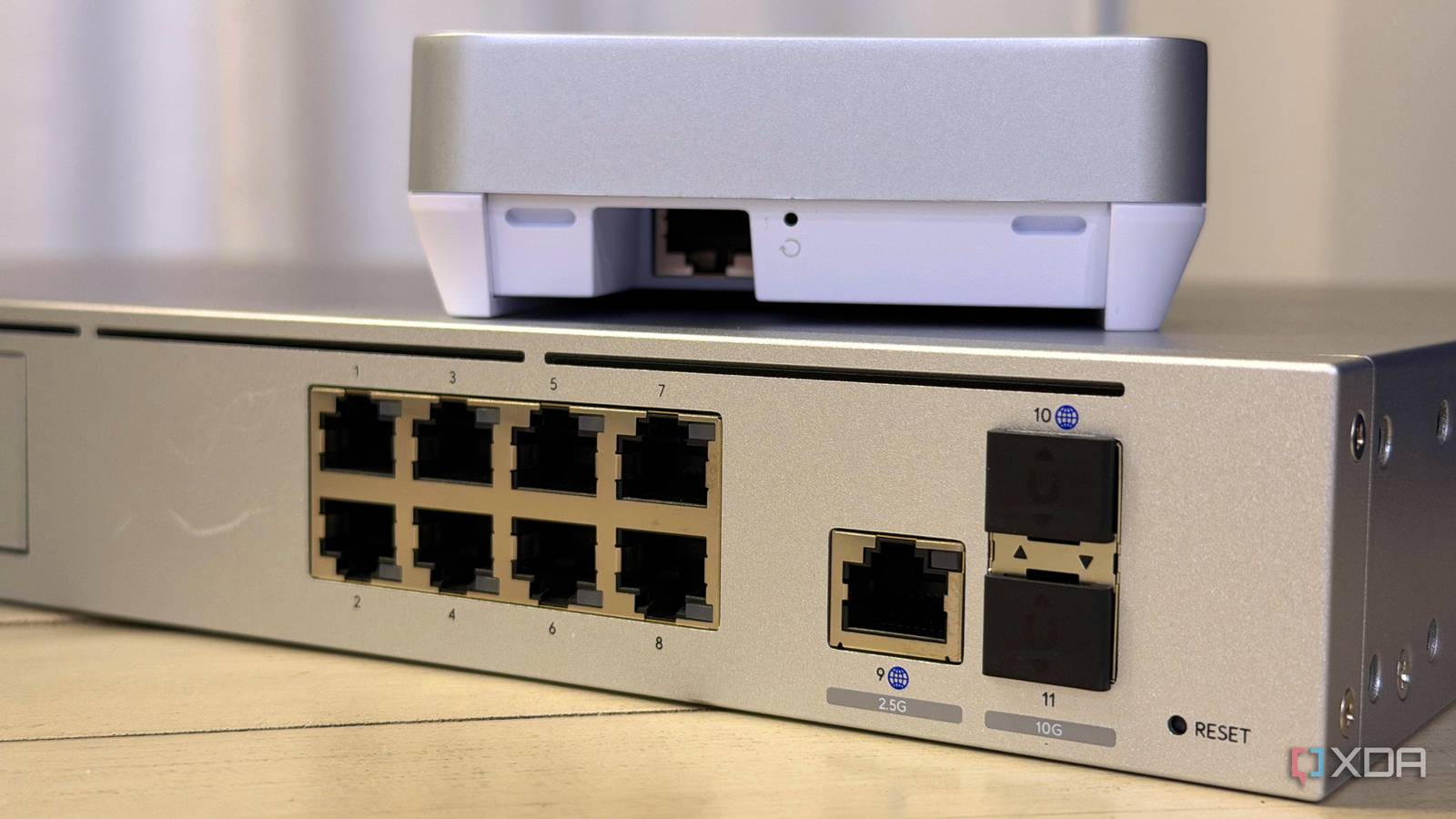
I’ve done DIY firewalls, consumer firewalls, and prosumer ones, and run without one before I knew any better. Currently, I’m using a UniFi Dream Machine Pro Max because after so many recommendations from everyone, I tried one and fell in love. Well, as much as anyone can love a shiny enclosed box.

The software is easy to use, offers tons of monitoring features I don’t have to spend time researching or installing, andjust works. Networking equipment has generally improved on user-friendliness over the years, and UniFi has been a large part of why. Having integrated NVR capability for networked cameras adds another layer to my home’s security, and I’d need a separate box to do that with most other routers.
Here’s the thing you need to understand. Hackers don’t care about you, just your data, or anyone’s data, really. They’re not even spending time hacking you, so get the outdated picture of 90s hacking movies out of your mind. They’re spending all their time finding exploits they can put into automated scripts, and let those scripts do all the work for them. Once those scripts find an attack surface, they’ll keep poking at exposed IP addresses to find a way through.
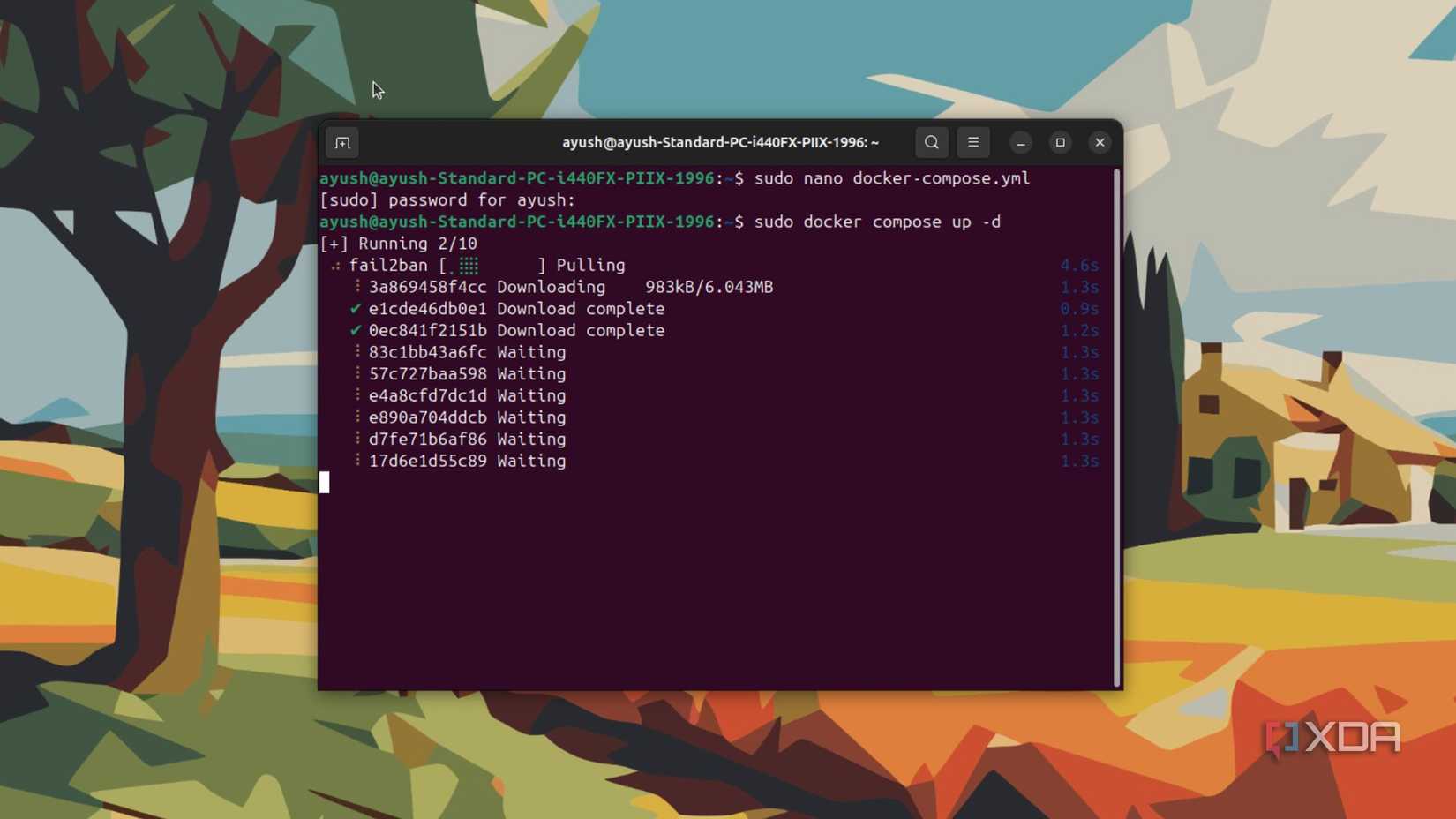
And we live in an age where almost everyone’s personal data has been leaked at least once. Username and password pairings are common enough that credential stuffing attacks work a dismaying percent of the time, and that’s why you need Fail2Ban.
Whether it’s the package for your router, or the UniFi script I use, this plugin monitors your firewall logs for unusual patterns, then automatically bans any external IP address behaving oddly. That keeps bots and other annoyances from running automated password testing on your network, and they’ll move on eventually.
If you’re not careful, your IoT devices could allow an attacker access to your home network.
IoT devices should be on their own network segment, so you can control the information they send out of your network. Not all of that data is inherently bad, but cloud services have been taken over before, and IoT devices are a favorite of hackers who like making botnets. It’s not really because of anything wrong with the devices, per se, but they tend not to have much storage space for security features, so you have to provide them.
You can connect them to Home Assistant for local control instead, and then you’ll have a smart home that works for you, without the risk of working against you in future.
I’ve long used MaxMind’s GeoIP lists to block entire countries, which lets you stop traffic from North Korea, Africa, Thailand, or anywhere else known to host spammers and hackers. I was so glad to see that it’s integrated into UniFi’s software natively in the Firewall & Security section, because if those countries are blocked from scanning your IP, they don’t know what’s there to poke at further.
All three of these rules keeps your home network safer, while running in the background and silently logging their progress. Sure, there are dozens of other useful firewall rules to consider using, but these three are tried and tested and known to work.
Why it matters
News like this often changes audience expectations and competitors’ plans.
When one player makes a move, others usually react — it is worth reading the event in context.
What to look out for next
The full picture will become clear in time, but the headline already shows the dynamics of the industry.
Further statements and user reactions will add to the story.